5 things you should know about DDoS attacks, outages, SSL, and web performance
It’s no surprise that online security is a burgeoning issue. 2014 has been a watershed year for the security industry, as cyberattacks reached a tipping point in terms of quantity, length, complexity, and targets.
Last week at Radware, we released our annual Global and Network Security Report. This report is based on data gathered from a survey of 330 organizations worldwide. The survey was designed to collect objective, vendor-neutral information about the issues organizations face when preparing for and fighting against cyberattacks.
The report gives a comprehensive and objective review of the past year’s cyberattacks from both a business and a technical perspective. It also offers best practice advice for organizations when planning for cyberattacks in 2015. But my favourite aspect of this report is the fascinating play-by-play insight into how today’s sophisticated attacks take place.
Key findings
- The internet pipe is the number one failure point in 2014.
- 19% of major reported attacks were considered “constant” by the targeted organization.
- The most commonly reported (15%) attack duration was one month. Yet 52% of respondents said they could only fight a campaign for a day or less.
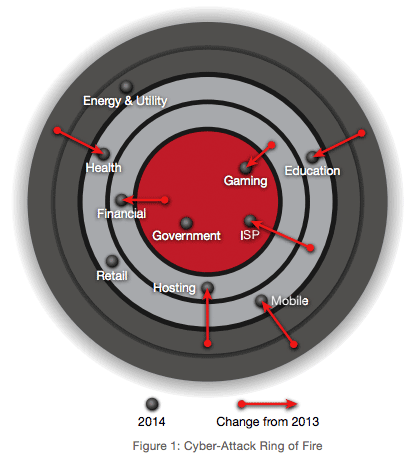
- Education, gaming, healthcare, and hosting/ISPs are the most highly targeted verticals.
- The Internet of Things brings an end to controlled endpoints and introduces new security threats.
- Software-defined network (SDN) DDoS capabilities are insufficient today and don’t allow customers to efficiently mitigate complex attacks.
Security and performance are incredibly closely entwined, and in some circles it’s a little-known fact that a cyberattack can have as much — if not more — impact on web performance as it has on downtime. Here are a few security/performance insights…
1. DoS/DDoS attacks are incorrectly associated only with service outage.
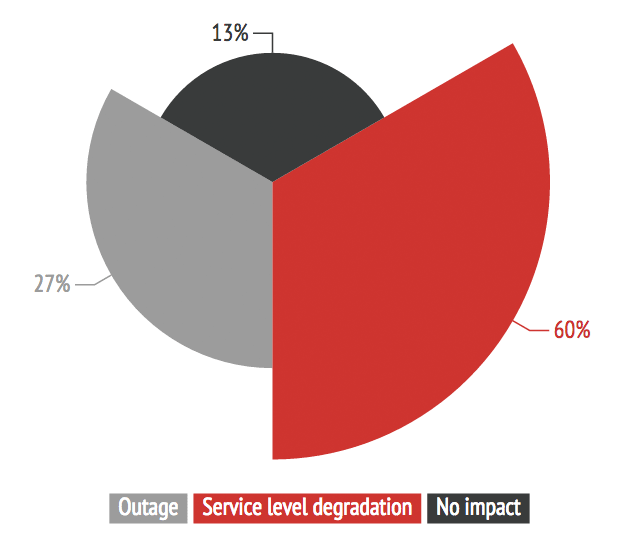
Many people believe that a successful DoS/DDoS attack results in a service outage. However, in our 2013 report, we revealed that the biggest impact of DoS/DDoS attacks was service level degradation, which in most cases is felt as service slowness. This finding has remained consistent throughout 2014.
2. Service degradation is felt more than twice as much as outages.
87% of respondents to past surveys have stated that they experience service level issues during security attacks – 60% encountered service degradation, while 27% experienced outages.
3. Slowdowns can hurt much more than outages.
As I’ve shared elsewhere, website slowdowns can have double the negative impact on an organization’s revenues as outages.
4. Gaming sites are extremely sensitive to speed degradation and outage.
A longstanding target of cyberattacks, gaming sites have historically been vulnerable when unsuccessful players sought revenge for their losses by pounding the site with whatever is at their disposal—which, in many cases, was a DDoS attack. In 2014, the experience of Radware’s ERT shows that attacks on gaming sites were longer and meaner. In all likelihood, these incidents didn’t result from lone angry users. The more likely sources of these sustained attacks are competitive saboteurs, extortion-driven attackers or other entities with large capacities.
5. SSL incurs potential performance risks.
A growing number of attacks target resources accessible over the Secure Sockets Layer (SSL). As a result, traffic is encrypted and defense mechanisms are often unable to inspect it. In these cases, defense mechanisms proxy the Transmission Control Protocol (TCP) payload without performing a real inspection. When defense mechanisms actually perform SSL decryption, they incur risk associated with heavy processing of the decryption and encryption. That processing places a significant burden on the SSL server-side computational and memory resources. Thus, many attackers add encryption to increase the strain rather than to actually evade detection.
So the question is: does this affect web performance? I asked Carl Herberger, Radware’s VP Security Solutions. His answer: “It depends.”
The SSL problem associated with cyberattacks stems from the issue in which security tools are generally opaque to the encrypted traffic and then can’t do inspection of the traffic for analysis. If they decrypt it and inspect it, then it causes (potentially) a performance issue. If they don’t decrypt it, they may have an even worse security issue on their hands.
Ultimately, “It’s a ‘damned if I do, damned if I don’t’ situation for performance and management.”
Conclusion
Organizations must be alert to the fact that security threats are at least as much a financial threat on the performance degradation front as they are on the outage front. And with more attacks targeting assets over SSL, there is an increased performance penalty incurred by heavy processing of decryption and encryption by defense solutions. As cyberattacks increase in length, complexity, and intensity, this will ultimately have a growing negative impact on end-user performance.
