DDoS 2.0: Hackers Getting a Taste of their Own Medicine
Cybercrime and hacktivism are on the rise and commercial and governmental organizations are common attack targets. But, based on recent evidence, an increasing number of cyber-attack targets are other attackers. That’s right – attackers attacking other attackers.
Recently, Radware security researchers have analyzed samples of a potentially new attack tool called “ddos.exe”. This tool challenges the concept of honor among thieves.
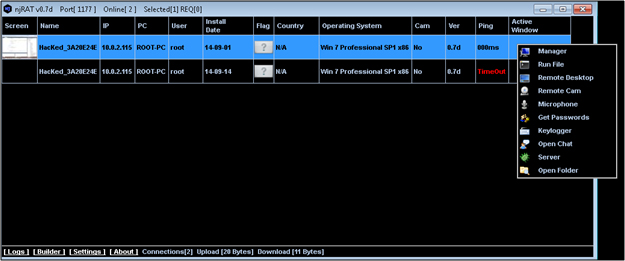
The alleged Denial of Service (DoS) attack tool, “ddos.exe” as implied by its name, is actually a new variant of NJRAT agent installer. How it works is that a victim is tricked to run the ddos.exe. They install the agent, which collects various information regarding the infected host, this information is then reported to the C&C and awaits for further instructions, such as: covert remote desktop, remote execute operating system commands, theft of keystrokes, file uploads, and remote camera control.
As normal NJRAT agents come with built-in anti-virus evasion techniques, the ddos.exe variant was tweaked further with additional commercial tools and proprietary code written to avoid this.
This sample seems similar to the case of Anonymous-OS, an operating system which was released by a group of hackers in 2012, later to be reported to have built in backdoors. So who is it that is interested in hacking and installing a Trojan in other attacker’s hosts?
Meet the attackers that are attacking the attackers
The main players could be hacktivists, cyber-criminals or law enforcement agencies.
Hacktivists
It is common practice for DoS groups to synchronize their targets and attacks. These groups often exchange DoS attack tools and it might seem legitimate from a hacktivist’s point of view that installation of a remote access tool on a “volunteered” host would mean a more effective way of utilizing resources for a DDoS campaign. In addition, it would also enable to ensure that this host can be used in future campaigns.
Cyber Criminals
For cyber criminals the normal motivations are to use the infected hosts to mine virtual currency or extract credentials from emails and websites in order to steal credit card information.
More interesting, just as Crypto Ransomware is widely used to blackmail legitimate users, there is no reason why cyber criminals would avoid blackmailing other cyber criminals. A cyber-criminal invests a lot in hiding his identity. A threat to disclose a cyber-criminal’s identity along with detailed pictures and recordings to the law enforcement can be quite effective.
Law Enforcement
Hacking hackers for the sake of national security is no myth. By gaining a foothold inside hacker groups and individuals, law enforcements can gather intelligence about the attackers, their motivations, and their targets. With this intel they can foil attacks before they begin, reach additional malicious hackers, and collect evidence that can be used in a court of justice.
The case of ddos.exe shows that the trend of attackers attacking attackers could be on the rise. One may think “great, let them have a taste of their own medicine.” But, this trend could actually expand the strength of big cyber-crook players with more resources, while it will push attackers to become smarter, stealthier, more cautious, harder to detect and eventually more dangerous.
To learn more about Radware’s Security Researchers, please visit: http://security.radware.com/ for information on recent threat alerts and cyber-attacks.