Could Your Network Survive APDoS or Hit-and-Run DDoS?
Can you guess where a network breach first occurs?
When a CISO asked this question during a recent business trip my answer was simple: “Sure! In the first line of defense.” Trying to improve my chances, I quickly added, “You know what, it’s when employees share on social networks and unintentionally provide puzzle pieces to potential perpetrators.”
“No,” he said. “It happens in the CISO’s mind. At the very moment they feel secure enough…”
That was an interesting statement and come to think about it, he did have a point. If threats are becoming more and more sophisticated, then security countermeasures have to evolve at the same pace and in the same direction.
What Will The Next Attack Look Like?
Many organizations still believe that if they upgrade their infrastructure, they can contain a DDoS attack – increase pipe capacity, add more cables, add network resources and components to be able to absorb a larger amount of traffic. Or alternatively – in extreme cases – dump traffic. It doesn’t have to be this way though and this will not stop multi-vector attacks.
Attackers have learned very well about the security solutions in the market and they have a good notion of the trends and heuristics that security experts follow. They are translating these lessons to more sophisticated tools, such as APDoS (Advanced Persistent Denial-of-Service) and Burst Attacks (AKA Hit-and-run DDoS). In their latest industry report, Radware’s Emergency Response Team (ERT) has indicated a growing use in these new formats.
Serious New Threats
APDoS is an ongoing DDoS attack that continues until the attacker stops the attack or the host server is able to defend against it. Since the attack is persistent, APDoS is essentially a potpourri of attack types and will most likely involve multiple vectors aimed at all network layers simultaneously.
A typical APDoS campaign combines massive network-layer DDoS attacks and focused application layer (HTTP) floods, followed by repeated SQLI and XSS attacks occurring at varying intervals. This can send up to tens of millions requests per second. Now imagine that, together with the good old volumetric attack in the form of large SYN Floods, and a relatively new vector – secure-SMTP (TLS over SMTP).
APDoS attacks can persist for weeks at a time, challenging the resources of even the most sophisticated security infrastructures.
Today’s threats drive demand for automated defenses and rapid analysis and mitigation. Think of your company for a second, is it prepared to mitigate an APDoS attack? Unfortunately, many organizations rely on dated techniques, like trying to synchronize multi-vendor solutions – this is a patchwork of solutions that require heavy manual intervention.
The rise of APDoS attacks represents an emerging threat demanding more advanced detection and mitigation and true partnership with DDoS mitigation service providers. Attackers are demonstrating more patience and persistence, leveraging “low and slow” attack techniques that misuse application resources rather than those in network stacks. Attackers are using evasive techniques to avoid detection and mitigation; including SSL-based attacks and changing the page request in an HTTP page flood attack.
APDoS will become a hacktivists’ preferred technique and it was used in the attack against ProtonMail.
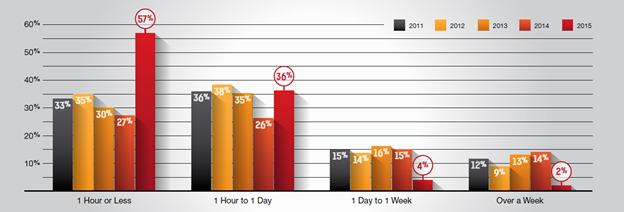
Burst Attacks aka “Hit-and-Run DDoS” use short bursts of high volume attacks in random intervals, spanning a time frame of days or weeks. These attacks lead to frequent and inconsistent disruptions in the network server’s SLA and can prevent legitimate users from using a service.
Hit-and-Run DDoS require access to extensive resources (computing power, botnet, applications) in order to launch high volume attacks in short bursts. Each burst can last short periods of time – sometimes several minutes – until the server goes down. The bursts may repeat every few hours during the span of the operation.
Bursts are also sometimes used as a test. An attacker will inject a few bad packets into a network to test if it is online and functioning. Hit-and-Run DDoS exploits anti-DDoS software and services that are used to defend against prolonged DDoS attacks. Activating such software can take longer than the actual attack, allowing a denial of service before DDoS protection can start to defend from the attack or learn its traffic pattern – since they too may be altered during the attack.
New Threats Require New Methods
Burst attacks are becoming more and more common. Though volumetric in nature, the volumes are on a much higher scale and this introduces the risk of Internet pipe saturation. A hybrid solution that includes on-premise protection to detect and mitigation the attacks in real-time, coupled with on-demand cloud protection for those volumetric attacks is the best approach here.
Analyzing recent Burst Attacks, Radware’s Emergency Response Team (ERT) indicated a growing use of automated, bot-based operations that generate large volumes of traffic in a short period of time. Maintaining these peaks over a long period of time will essentially create an APDoS.
Returning to that CISO’s approach, my conclusion is that just like the perpetrators that are improving their offensive tools we need to keep our protective systems smart and adaptive.

